IT leaders are rightly concerned about the status of their tech stacks, particularly as those stacks become more complex. While configuration drift, access control and shadow IT are not new challenges, they’re being amplified by agentic AI and multi-cloud environments.
With the growing frequency of cyberattacks, arguably everyone’s job includes security, but security is often sacrificed for speed. IT departments are under constant pressure to move faster, fix mistakes and accomplish more with less.
Meanwhile, some business leaders are questioning investments in cybersecurity. For example, Mike Lyborg, CISO at AI security automation company Swimlane, once faced that exact problem at a previous employer: On the chopping block were email and gateway protection, collaboration tech and tooling. He resigned because he didn’t have what he needed to do his job. Subsequently, the company’s email was compromised, resulting in the loss of several hundred thousand dollars to a bad actor.
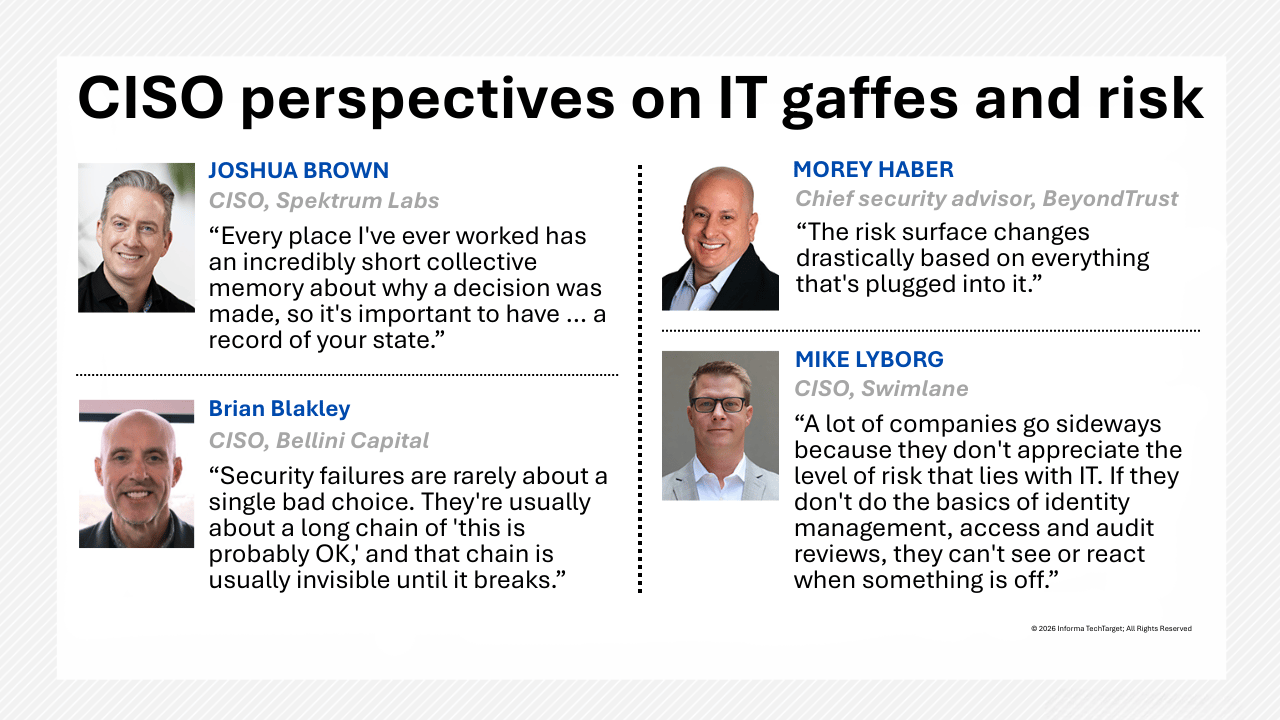
“A lot of companies go sideways because they don’t appreciate the level of risk that lies with IT,” Lyborg said. “If they don’t do the basics of identity management, access and audit reviews, they can’t see or react when something [is off].”
Cybersecurity basics still matter
Catastrophic incidents typically aren’t the result of sophisticated attacks. Instead, they stem from small mistakes or oversights.
Brian Blakley, CISO at investment firm Bellini Capital, said a business failed because of a performance-driven configuration error. Specifically, users had complained that the network was slow, so IT temporarily relaxed a control and forgot about it. Several weeks later, an attacker was moving laterally across systems. “Security failures are rarely about a single bad choice. They’re usually about a long chain of ‘this is probably OK,’ and that chain is usually invisible until it snaps,” Blakley said.
Worse, there’s a tendency to hide issues that have arisen rather than sharing them with the team so others can learn, according to Randy Dougherty, CIO at AI-powered cybersecurity company Trellix.
Configuration drift and misconfigurations
Misconfigurations have opened the door to many breaches and accidental data exposure. An example of that was when PetCo exposed sensitive user data, including Social Security numbers, driver’s license numbers and financial information, as the result of an app setting. And unfortunately, even sound configurations can drift over time.
“At a previous company, I used to see a lot of cases where teams would spin up something with good intentions, but they didn’t spend a little time either locking it down or adding a configuration setting,” said Joshua Scott, CISO at streaming data lake platform Hydrolix.
Swimlane constantly scans infrastructure and configurations to see what’s being applied, even to firewalls.
Joshua Brown, CISO, at AI-first cyber resilience company Spektrum Labs and former global CISO at H&R Block, recommends approaching cybersecurity from a risk management standpoint to reduce risk to an acceptable level.
“Every place I’ve ever worked has an incredibly short collective memory about why a decision was made, so it’s important to have complete visibility and a record of your state, including the decisions you make around that state over time,” Brown said.
That documentation can help counter the instinct to assign blame — often to the CISO — when something goes wrong.
AI expands the cybersecurity and attack surface
Many organizations still struggle with data management, yet they’re racing to adopt AI. As if their tech stacks weren’t already complicated enough, the ratio of non-human to human identities continues to grow, with 2025 estimates varying greatly — from 43:1 to 144:1.
Convenience and speed are often at odds with cybersecurity, as demonstrated by a critical ServiceNow AI platform vulnerability last fall. The company issued the same credential to every third-party service that was authenticated to its Virtual Agent API. Worse, a flaw allowed user impersonation using only an email address.
Agentic AI expands the attack surface because it acts on behalf of humans. So, for example, if a personal assistant like Microsoft Copilot has access to email, a vulnerability exploit might affect the AI engine as opposed to the mail server.
“The risk surface changes drastically based on everything that’s plugged into it,” said Morey Haber, chief security advisor at identity security protection company BeyondTrust.
Non-human identities should be assigned and traceable, so activity can be attributed if something goes wrong. These identities also should be treated as a corporate asset.
One potential pitfall to consider is contractual data usage clauses. Without proper data governance, data usage may be unauthorized, even if it’s aggregated or anonymized. “It starts with data governance, understanding what data retention, classification and handling look like, and [having] proper controls in place that mirror the risk that the business is willing to accept,” Bellini Capital’s Blakley said.
At Swimlane, agentic AI has a human in the loop. For example, if an AI agent changes a line of code, a human reviews it to ensure the change is proper.
Shadow IT and shadow AI risks
Shadow IT is alive and well, and it’s taken a scary turn for the worse: Individuals are uploading company information into their personal AI accounts to get their jobs done faster. Though some IT leaders have tried to manage shadow IT by creating internal app marketplaces or providing guardrails for tech adoption, nothing works perfectly all the time.
Shadow IT was to blame when a Java vulnerability led to the exfiltration of authentication data from 140,000 Oracle Cloud tenant users. In that case, cloud instances had been forgotten, unauthorized or unmanaged.
Hydrolix’s Scott once witnessed firsthand what can go wrong when AI notetakers attend meetings. During a former employer’s all-hands meeting, details of the company’s roadmap were revealed, while the notetaker transcribed what was said and captured the screenshots that were shared to a public link.
Over-privileging is a common challenge with interconnected systems, and it often takes the form of failing to revoke credentials in a timely fashion. BeyondTrust’s Haber experienced this firsthand early in his career when a partner organization failed to revoke access that enabled users to download enterprise software.
“The most common mistake is something was installed, it was convenient and then it became a security risk,” Haber said.
Swimlane tagged all its CRM data so if someone attempts to login to Salesforce without the right permissions, they can’t log in, no matter how many IT tickets they generate. While it takes a couple of years to complete such a project, hardening the data stores and endpoints helps mitigate risk. It also lessens the blow of a compromise.
The demeanors of the CIO and CISO also affect shadow IT, particularly when those functions become synonymous with “no.” Spektrum’s Brown said he wants to know what users are trying to do, so he can provide an acceptable solution.
“I think the idea of control is a false one. Even if they understand what could happen, they’re going to do whatever is the most efficient way for them to get their job done so security needs to be a partner in defining what those pathways are not,” Brown said.
Identity and access management gaps
In today’s modern IT environments, just about everything is connected to something else. That means bad actors may be able to exploit a vulnerability and move through the network to exfiltrate data or cause other harm. Therefore, it’s critical to understand where handoffs occur or should occur, why, and what the appropriate permission levels should be.
Blue Shield of California accidentally exposed the private data of 4.7 million customers when a Google Analytics misconfiguration shared the data with Google Ads. The unauthorized data usage persisted for nearly three years until the connection was finally severed.
While working for a former company, BeyondTrust’s Haber said a secretary’s email account was compromised and used to distribute child pornography throughout the company. By law, the FBI had to be notified and all the content on devices needed to be scrubbed before they could be brought back online. “I’m a firm believer in formalized change control so IT does not introduce anything unless it’s properly signed off by teams,” Haber said.
A lot of organizations have not taken the time to confirm that their data flows properly. By keeping the channels of communication open and talking through such things, CISOs can uncover IT mistakes and unwanted behavior, such as a marketing team member downloading customer data from an internal database, uploading it to Google Drive, exporting it and uploading it to HubSpot so a third-party contractor can create a mailing list.
“If you don’t understand the data flows, how can you put in the right controls and technology to support that?” Blakley said.


