Software teams do not struggle because they write code too slowly. They struggle because code moves too slowly after it is written. Manual handoffs, late testing, and risky deployments create delays. Then small bugs turn into release problems. That is why many teams ask what is a ci cd pipeline. The practical answer is simple. A CI/CD pipeline is the system that moves code from commit to release through repeatable automation. It helps teams test earlier, deploy with less drama, and learn faster from production.
The shift is not small. GitHub reported 11.5 billion total GitHub Actions minutes in public projects in 2025. CircleCI also based its 2025 delivery research on over 14 million workflows. Modern delivery now depends on automation at scale, not on release-day heroics.

What Is A CI/CD Pipeline?

A CI/CD pipeline is an automated workflow that replaces manual steps with pipelines that build, test, and deploy software reliably. It turns every code change into a controlled process. Instead of waiting for a big release, teams let automation check each change as it moves forward.
The pipeline usually starts when a developer pushes code to a shared repository. Then it runs a sequence of steps such as linting, building, testing, packaging, releasing, deploying, and monitoring. OWASP describes CI/CD as a set of largely automated processes used to build and deliver software. That definition matters because CI/CD is not one tool. It is a delivery system made of triggers, rules, environments, and feedback loops.
Good pipelines do three jobs at once. First, they reduce manual work. Second, they create a reliable path from code to production. Third, they make software delivery measurable. Teams can see where builds fail, where tests slow down, and where releases need stronger controls.
That is why the word pipeline fits so well. Code does not jump straight from a laptop to production. It flows through checkpoints. Each checkpoint protects quality, speed, and trust.
What Do CI And CD Mean?
1. What Is Continuous Integration (CI)?
Continuous integration means developers regularly merge their code changes into a central repository, after which automated builds and tests are run. In simple terms, developers integrate early and often instead of saving work for a painful merge later.
CI solves a common problem. When people work in isolation for too long, code drifts apart. Merge conflicts grow. Hidden bugs pile up. Release branches become fragile. CI cuts that risk by forcing small changes through fast validation.
A healthy CI practice usually includes a few habits:
- Small and frequent commits.
- Automated builds on every push or pull request.
- Fast unit and integration tests.
- Clear failure signals when something breaks.
- A shared main branch that stays usable.
CI is not only about tooling. It also shapes team behavior. Developers learn to break work into smaller units. Reviewers get cleaner pull requests. Teams spot defects closer to the moment they were introduced.
2. What Is Continuous Delivery (CD)?
Continuous delivery is the process of automating build, test, configuration, and deployment from a build to a production environment. It takes the validated output from CI and pushes it toward release readiness.
The key idea is readiness. A team using continuous delivery keeps software in a state that can go live at any time. Code passes through staging, approvals, environment checks, and release rules in a repeatable way. Humans may still decide when production deployment happens, but the deployment itself should not depend on manual scripts and guesswork.
Continuous delivery helps teams reduce release friction. Instead of bundling many changes into one risky event, they push smaller updates through the same release path again and again. That makes problems easier to isolate and easier to reverse.
It also supports safer rollout patterns. Teams can deploy to staging first, test smoke checks, expose only a small user segment, and then expand the release if metrics stay healthy.
3. Continuous Delivery Vs Continuous Deployment
These two terms sound close because they are close. However, they are not identical. Atlassian explains the final step clearly: every change that passes all stages of your production pipeline is released to your customers in continuous deployment.
| Practice | What Happens | Human Approval |
|---|---|---|
| Continuous Delivery | The pipeline builds, tests, and prepares a release for production. | Usually yes, before the final production step. |
| Continuous Deployment | The pipeline builds, tests, and deploys to production automatically. | No, unless a failed rule blocks the release. |
So the difference sits at the end of the flow. Delivery means the software stays ready to release. Deployment means the software goes live automatically after it passes the rules.
Many companies start with continuous delivery. That path gives them strong automation while still leaving room for business approvals, support coordination, or compliance review. Teams move to continuous deployment later when their tests, controls, and monitoring become strong enough.
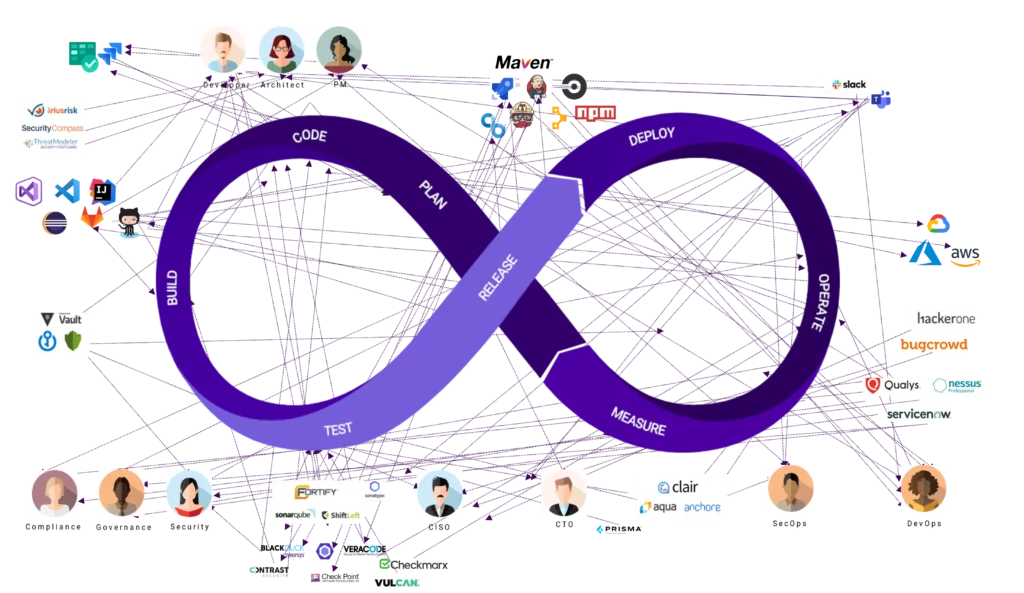
How CI/CD Pipelines Relate To DevOps
CI/CD is not the same thing as DevOps. It is one of the clearest ways to put DevOps into practice. Google Cloud defines DevOps as the organizational and cultural movement that aims to increase software delivery velocity, improve service reliability, and build shared ownership among software stakeholders.
That definition matters because DevOps is broader than automation. DevOps changes how development, operations, security, and product teams work together. It promotes shared responsibility, quick feedback, and continuous improvement.
CI/CD gives DevOps a working engine. It turns those ideas into a repeatable release process. Without CI/CD, DevOps often stays a slogan. With CI/CD, teams can prove that they deploy faster, test earlier, and recover with less confusion.
The relationship works like this:
- DevOps sets the operating model.
- CI/CD provides the delivery workflow.
- Infrastructure as code, observability, and policy controls support the pipeline.
- Monitoring closes the loop after release.
So when leaders ask whether they need DevOps or CI/CD, the better answer is both. DevOps shapes how the team collaborates. CI/CD shapes how the software moves.
How A CI/CD Pipeline Works
1. Code Changes Trigger The Pipeline
A pipeline usually begins with an event in version control. GitHub explains that you can configure a GitHub Actions workflow to be triggered when an event occurs in your repository. That event might be a push, a pull request, a tag, or a merge to the main branch.
This trigger matters because it removes delay. Teams do not wait for someone to remember the next step. The pipeline reacts right away. That gives developers quick feedback while the change still feels fresh.
Most teams use different triggers for different goals. A pull request may run linting, unit tests, and preview builds. A merge to main may build the release artifact and deploy to staging. A version tag may deploy to production.
Good trigger design keeps the pipeline fast and relevant. It does not run every expensive test on every minor event. Instead, it runs the right checks at the right stage.
2. Build And Test Steps Validate The Release
After the trigger fires, the pipeline builds the application and runs automated checks. This stage often includes dependency installation, compilation, packaging, unit tests, integration tests, code quality checks, and artifact creation.
Fast feedback is the goal. CircleCI found a median workflow duration of 2 minutes and 43 seconds in its 2025 report, while many teams still ran far longer workflows than the recommended benchmark. That gap shows why pipeline design matters. When feedback comes too late, developers lose context and defects cost more to fix.
Build and test steps should answer one simple question: can this change move forward safely? If the answer is no, the pipeline should fail fast and explain why. Teams should not guess whether a release is ready.
That is also why test layering helps. Unit tests catch logic errors early. Integration tests check service boundaries. End-to-end tests confirm the user journey. Security and dependency scans add another quality gate before release.
3. Deployment Automation Moves Code Across Environments
Once the artifact passes validation, the pipeline promotes it across environments. A common path is development to staging to production. The exact path varies, but the principle stays the same. The same validated build should move forward with as little manual rework as possible.
Strong deployment automation reduces environment drift. Teams avoid the classic problem where code works in staging but fails in production because someone changed settings by hand. Instead, the pipeline applies the same deployment logic every time.
Modern teams also use safer rollout methods. They may push to a canary group first, route only part of the traffic to the new version, or use blue-green environments for quick cutover and rollback. These patterns help teams limit blast radius while still shipping often.
This is where continuous delivery becomes visible to the business. Releases stop feeling like special events. They become normal, repeatable operations.
4. Monitoring And Feedback Improve Future Releases
A release is not the end of the pipeline. It is the start of feedback. Teams need logs, metrics, traces, alerts, and user signals to see whether the new version behaves as expected.
Monitoring turns production into a learning system. If latency rises, error rates spike, or business conversions fall, the team can react fast. They can roll back, disable a feature flag, or tighten a weak test that failed to catch the issue earlier.
This feedback loop is one reason CI/CD improves over time. Every incident can refine the pipeline. Teams add new checks, shorten slow steps, and remove fragile manual handoffs.
That ongoing learning matters because software delivery is never static. Systems grow. Teams change. Requirements shift. The pipeline must keep evolving with them.
Key Stages Of A CI/CD Pipeline

Most pipelines share the same core stages, even when the tools differ. The table below shows the common flow.
| Stage | Main Goal | Typical Output |
|---|---|---|
| Source | Capture versioned code and trigger rules | Commit, branch, pull request, or tag |
| Build | Turn source into a runnable artifact | Binary, package, or container image |
| Test | Validate quality, behavior, and security | Pass or fail results |
| Release | Version, sign, and approve the artifact | Release candidate |
| Deploy | Promote the artifact to target environments | Running application |
| Monitor | Track health and user impact | Metrics, logs, alerts, and insights |
1. Source
The source stage starts with version control. Teams store code, pipeline files, and often infrastructure definitions in the same repository or in connected repositories. This stage creates traceability. Every build should map back to a known commit, author, review, and change record.
Strong source practices keep the pipeline clean. Branch rules, pull request reviews, signed commits, and protected main branches all reduce chaos before automation even begins.
2. Build
The build stage converts source code into a package that environments can run. That may be a compiled binary, a Java archive, a Node package, or a container image. The build should stay reproducible. The same input should create the same output.
This stage often includes dependency resolution and artifact packaging. For cloud-native teams, it may also build and tag a container image and push it to a registry.
3. Test
The test stage checks whether the build deserves promotion. Teams usually combine several kinds of tests here. Unit tests verify functions. Integration tests verify connections. End-to-end tests verify user flows. Security tests check dependencies, secrets, images, and infrastructure definitions.
The best pipelines balance depth and speed. Not every test belongs in the first minute. However, every change should meet a clear quality bar before it moves ahead.
4. Release
The release stage prepares a version for controlled deployment. Teams may add version numbers, create changelogs, sign artifacts, store metadata, or apply an approval gate. This stage is useful because it separates build success from release readiness.
For regulated teams, release also creates an audit trail. Teams can show what changed, who approved it, and what artifact went live.
5. Deploy
The deploy stage places the release into a target environment. That may be a staging slot, a virtual machine, a serverless platform, or a Kubernetes cluster. Good deployment automation keeps the action predictable and reversible.
Deployment also includes environment rules. Teams may inject secrets at runtime, run database migrations, start smoke tests, or block rollout if health checks fail.
6. Monitor
The monitor stage tracks system health and business impact after release. Teams watch error rates, latency, resource use, and user behavior. If the release causes harm, the pipeline should support rollback or rapid remediation.
This stage often gets less attention than build and deploy. That is a mistake. A pipeline without monitoring cannot tell the team whether a release actually succeeded.
Benefits Of CI/CD Pipeline
A strong pipeline does more than automate tasks. It changes delivery economics. It lowers waiting time, shrinks batch size, and makes quality checks repeatable.
Faster Release Rates. CI/CD removes the stop-and-start pattern of manual releases. CircleCI reported that the most productive organizations on its platform averaged 3,762 daily workflow runs, which shows how much throughput automation can support when teams reduce delivery friction.
Improved Software Quality. Frequent integration and repeatable testing catch defects closer to the change that caused them. Main-branch success rates, recovery speed, and test stability become visible instead of hidden. That visibility helps teams improve release quality in a disciplined way.
Lower Risk. Smaller changes are easier to review, test, deploy, and roll back. Teams no longer bet the whole release on one giant batch of mixed features and fixes. They release smaller pieces through the same safe path.
Increased Productivity. Tooling sprawl wastes engineering time. GitLab found that 70% of respondents said developer onboarding in their organizations takes more than a month. Standardized pipelines reduce that friction because new developers do not need to learn a maze of manual release steps before they can contribute safely.
These benefits reinforce each other. Faster feedback improves quality. Better quality reduces rework. Lower rework creates more time for actual product work.
How CI/CD Pipelines Support Security
CI/CD can improve security, but only when teams design it that way. OWASP warns that CI/CD services provide an efficient path to reaching an organization’s crown jewels. That is why secure pipelines matter as much as fast pipelines.
Automated security checks in the pipeline. Teams can run static analysis, dependency scanning, secret detection, container image scanning, and infrastructure-as-code checks before a release moves ahead. This approach catches common problems while developers still work in the same context.
Early detection of vulnerabilities. Security becomes stronger when checks happen on pull requests and builds, not only during a later audit. GitHub reported 30% faster fixes of critical severity vulnerabilities in 2025. That improvement shows what happens when automation and remediation workflows get tighter.
Better policy enforcement before production release. Pipelines can require approvals, signed artifacts, branch protections, minimum test coverage, or environment-specific rules. They can also block deployments when permissions look unsafe or when a critical dependency issue remains unresolved.
Safer delivery through integrated testing and compliance checks. Security works best when it joins the normal release path. Teams should not bolt it on later. Secure credential handling, artifact integrity validation, least-privilege runners, and strong flow controls all belong inside the pipeline design itself.
In short, CI/CD supports security when teams treat the pipeline as production infrastructure, not as a helper script.
No single tool stack fits every team. Some teams want tight integration with their source platform. Others need strong on-prem support, complex approvals, or cloud-native delivery patterns. The right choice depends on team size, compliance needs, hosting model, and existing skills.
1. Source Control Tools
Source control tools manage repositories, pull requests, branch rules, and event triggers. Common choices include GitHub, GitLab, Bitbucket, and Azure Repos. The key requirement is not the brand. It is the ability to support reviews, permissions, auditability, and reliable pipeline triggers.
Teams should keep pipeline files under version control too. That makes the delivery process reviewable and reproducible. When pipeline rules live beside code, change history becomes much easier to trace.
2. CI/CD Automation Tools
Automation tools run the workflow itself. Common options include GitHub Actions, GitLab CI/CD, Jenkins, CircleCI, and Azure Pipelines. These platforms differ in runner models, integrations, caching, secrets handling, governance features, and self-hosting support.
When choosing one, compare these factors:
- How close the tool sits to your repository and issue workflow.
- How easy it is to manage reusable pipeline templates.
- How well it handles secrets, permissions, and approvals.
- How much control you need over runners and infrastructure.
- How strong its reporting and debugging experience feels.
Configuration matters as much as product choice. Teams should define pipelines as code, keep steps modular, and make failures readable. A confusing pipeline slows delivery even when the platform is powerful.
3. Testing Tools
Testing tools validate different layers of the system. Unit test tools may include JUnit, pytest, or Jest. Browser and end-to-end testing may use Playwright or Cypress. API checks may use Postman or Newman. Security testing may add dependency, secret, IaC, and image scanners.
The main goal is coverage that matches risk. A simple web app does not need the same checks as a regulated platform. However, every pipeline needs a clear test strategy. Teams should know which checks run on pull requests, which run before staging, and which run before production.
4. Container And Deployment Tools
Modern teams often package applications with Docker and deploy them through tools such as Kubernetes, Helm, Argo CD, or cloud-native deployment services. CNCF reported that 82% of container users now run Kubernetes in production. That helps explain why container-aware pipelines matter so much today.
These tools support image builds, environment promotion, rollout policies, and rollback logic. For cloud-native systems, deployment tooling often decides whether releases stay safe under scale.
Teams should also think about configuration drift. Using deployment manifests, templates, and GitOps-style promotion reduces surprise changes between environments.
5. Monitoring Tools
Monitoring tools close the release loop. Teams often combine logs, metrics, traces, dashboards, and alerting. Common choices include Prometheus, Grafana, Datadog, New Relic, CloudWatch, and OpenTelemetry-based stacks.
The pipeline should connect to these signals. A deployment without health visibility is only half a release. Good monitoring lets teams decide whether to continue rollout, pause, or roll back based on evidence instead of hope.
CI/CD Pipeline Example
1. Example For A Web Application
Imagine a team that maintains an eCommerce web app with a React frontend and a Node.js backend. The team stores code in Git. Every pull request triggers a CI workflow.
The flow may look like this:
- A developer opens a pull request.
- The pipeline installs dependencies, runs linting, and executes unit tests.
- If checks pass, it builds a preview version for review.
- After merge, the pipeline builds the production artifact and deploys it to staging.
- Smoke tests verify core paths such as login, cart, and checkout.
- A release manager approves the production deployment.
- The pipeline deploys the same artifact to production and watches error metrics.
This example shows why CI/CD reduces release stress. The team does not rebuild by hand for production. It promotes the same tested output forward. If checkout errors spike after release, the team rolls back quickly and inspects the exact build that caused the issue.
2. Example For A Cloud-Native Application
Now imagine a cloud-native payment service built with Go and deployed on Kubernetes. The team uses container images and Git-based deployment rules.
A practical pipeline may work like this:
- A commit to the main branch starts the build.
- The pipeline compiles the service and runs unit and integration tests.
- It builds a container image, scans it, and pushes it to a registry.
- It updates the deployment manifest for staging.
- Argo CD or a similar tool syncs the cluster to the new desired state.
- Health checks and service metrics decide whether rollout continues.
- If the release stays healthy, the pipeline promotes the version to production.
This setup fits modern distributed systems well. It keeps deployment logic declarative. It also supports progressive rollout, policy checks, and fast rollback when the new pod version degrades service health.
FAQs About CI/CD Pipelines
1. What Is The Difference Between CI And CD?
CI focuses on integrating code changes frequently and validating them with automated builds and tests. CD takes the validated output and moves it toward release or deployment through automated delivery steps. CI checks that the code works together. CD checks that the code can move safely toward users.
2. What Is The Difference Between DevOps And CI/CD?
DevOps is the broader operating model. It covers culture, team collaboration, shared ownership, reliability, and feedback. CI/CD is one delivery practice inside that model. DevOps tells teams how to work together. CI/CD gives them an automated path to ship software.
3. What Are The Core Principles Of CI?
The core principles are simple:
- Integrate small changes often.
- Keep code in a shared repository.
- Run automated builds and tests on every change.
- Fix broken builds fast.
- Keep the main branch healthy and releasable.
These principles reduce integration pain and create faster feedback.
4. Is CI/CD Used In Frontend Or Backend Development?
Yes. Teams use CI/CD in frontend, backend, mobile, data, and infrastructure work. Frontend teams use it for linting, browser tests, preview deployments, and static builds. Backend teams use it for API tests, package builds, container images, and service deployments. The pattern stays the same even when the stack changes.
A CI/CD pipeline is not just a DevOps buzzword. It is the release path that lets modern teams turn code into dependable delivery. When teams design that path well, they ship smaller changes, catch problems sooner, protect production better, and learn faster after every release.
If a team still handles releases through manual checklists, scattered scripts, and last-minute approvals, that is usually the biggest improvement opportunity. Start with one repeatable pipeline, keep it visible, and improve it every sprint. That is how software delivery becomes reliable instead of stressful.
Conclusion
A strong answer to what is a ci cd pipeline is simple. It is the delivery system that helps teams ship smaller changes, test earlier, and release with less risk. Speed matters, but confidence matters more. When teams build pipelines well, they reduce fragile handoffs, catch issues sooner, and turn releases into a repeatable process instead of a stressful event.
At Designveloper, we build that reliability into products from day one. We are a software partner in Vietnam founded in 2013, with 100+ successful projects for 50+ clients worldwide and a 110-strong team across development, UI/UX, QA, and consulting. That experience comes from real product delivery on Lumin, Bonux, Walrus Education, and Joyn’it, along with our broader work in custom software, web app development, mobile app development, and AI-powered business software.
When your business needs faster and safer releases, we can help you design the right CI/CD pipeline for your product, team, and infrastructure. We do not treat delivery as an afterthought. We build it into the product, the workflow, and the release process, so your code can move from commit to production with more control and fewer surprises. Contact us to plan a delivery pipeline that supports real growth, not just one more deployment.


