In the 1979 Sci-Fi classic “Alien,” Ellen Ripley refuses to break protocol, recognizing that an unvetted threat allowed past the airlock could endanger the entire ship.
Had the crew members of the USCSS Nostromo followed her lead, most of them would likely have survived. Instead, they were up against a threat that evolved faster than they could respond in a coordinated way — a cinematic nightmare made real in recent weeks as AI-imbued security systems like Anthropic’s Mythos show how attacks can slip through controls and outrun traditional defenses at machine speed.
For CIOs, the emergence of Mythos and its ilk is a call to rethink the step-by-step protocols of vulnerability management for a reality in which attacks are automated and executed at machine speed before most teams can respond.
Mythos testing exposes both zero-day and longstanding vulnerabilities
Earlier this month, Anthropic launched Claude Mythos Preview, a general-purpose language model to be used within Project Glasswing, which includes a select group of about 50 open source, technology and cybersecurity companies — including AWS, Apple, Palo Alto Networks and Nvidia — tasked with testing the AI model.
Mythos is being used by Anthropic and Project Glasswing to identify and exploit zero-day vulnerabilities in open source codebases. Anthropic’s own testing of Mythos uncovered that the AI is “capable of identifying and then exploiting zero-day vulnerabilities in every major operating system and every major web browser when directed by a user to do so.” The Mythos tests even identified some vulnerabilities that are over 20 years old. In addition, less than 1% of potential vulnerabilities uncovered by Mythos have been fully patched by their maintainers, according to Gartner. Over 99% of vulnerabilities revealed by Mythos haven’t been patched.
For its part, Anthropic is optimistic that the cybersecurity industry can adapt to AI-based threats. By releasing Mythos to a select group first, the company has argued that it is giving cybersecurity defenders a head start on patching vulnerabilities before similar AI models are widely available.
“Once the security landscape has reached a new equilibrium, we believe that powerful language models will benefit defenders more than attackers, increasing the overall security of the software ecosystem. The advantage will belong to the side that can get the most out of these tools,” Anthropic said.
AI collapses the window between vulnerability discovery and exportation
While Mythos is currently not generally available, bad actors are increasingly using AI to “develop more sophisticated AI-malware and accelerated adaptive attack campaigns,” according to a report by research firm Omdia. As a result, the increase in AI-based attacks shakes up the traditional approach to vulnerability management.
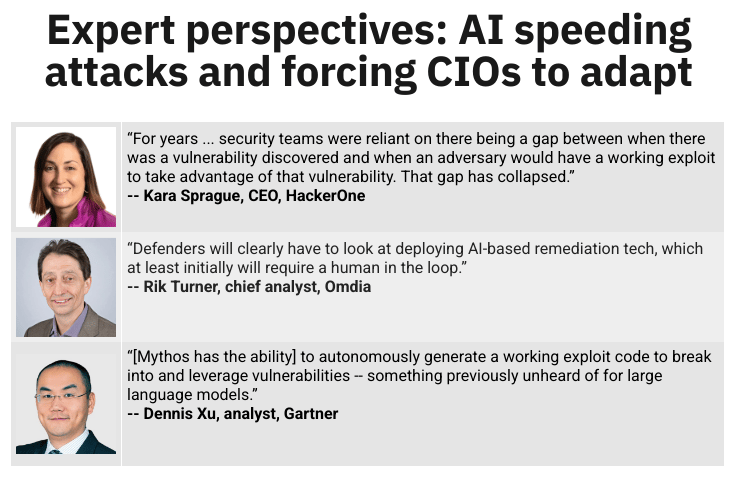
As bad actors use AI to autonomously generate code to hack into organizations, there’s far less time to address vulnerabilities. “For years in the space of vulnerability management and exposure management, security teams were reliant on there being a gap between when there was a vulnerability discovered and when an adversary would have a working exploit to take advantage of that vulnerability, and that gap has collapsed,” Kara Sprague, CEO of cybersecurity operations technology company HackerOne, told InformationWeek.
In addition, Mythos can autonomously generate exploits — it can “chain together and create complex exploits, and build exploits off of what might otherwise be considered lower-severity findings,” Sprague said.
That capability to generate working exploit codes to breach enterprise systems is previously unheard of by frontier LLMs, said Dennis Xu, an analyst at Gartner.
The speed with which vulnerabilities can now be identified and exploited makes vulnerability management much more challenging. Patching vulnerabilities has historically already been a time-consuming effort because it’s typically an operations function, Xu explained. Organizations must run tests to ensure the patch doesn’t break any software systems or customer-facing platforms. Companies then must determine when to implement a patch to avoid disrupting business operations.
“Because defenders generally need to retool their teams, their operations and their processes, in addition to just adopting technology, their adoption on at least the company side tends to be slower than attackers are moving,” Sprague explained.
Solutions to AI-based threats
There’s no time to waste in adapting cybersecurity strategies to account for AI-based threats. While Mythos is currently available to only a select group of companies that are part of Project Glasswing, other Frontier AI models will likely catch up to Mythos in the next three to six months, Xu said. And there’s always the possibility that new AI models will be generally available.
In the short term, CIOs and CISOs can keep a close eye on the cybersecurity companies participating in Project Glasswing — such as Cisco, Palo Alto and Zscaler — and when those companies release a patch, deploy it immediately within their own organization, he added.
In the long term, Xu said, vulnerability management providers can support enterprises by using AI models to identify software vulnerabilities more proactively. CIOs and CISOs can reexamine their vulnerability management cycle and should look for more ways to automate and speed up the remediation process.
Omdia Chief Analyst Rik Turner echoed Xu’s suggestion. “Defenders will clearly have to look at deploying AI-based remediation tech, which at least initially will require a human in the loop,” he said.
Sprague also recommended using AI to thwart attacks from bad actors. She explained that organizations should consider utilizing cybersecurity platforms that can weed out false positives and validate if a vulnerability is exploitable.


